💡 Claude Mythos and the Next Shift in Cyber Security
Key Points: Claude Mythos and the Next Shift in Cyber Risk
- Anthropic’s new model “Claude Mythos” is a highly advanced AI focused on software security, capable of autonomously finding, chaining, and exploiting vulnerabilities at a level comparable to elite cyber attackers.
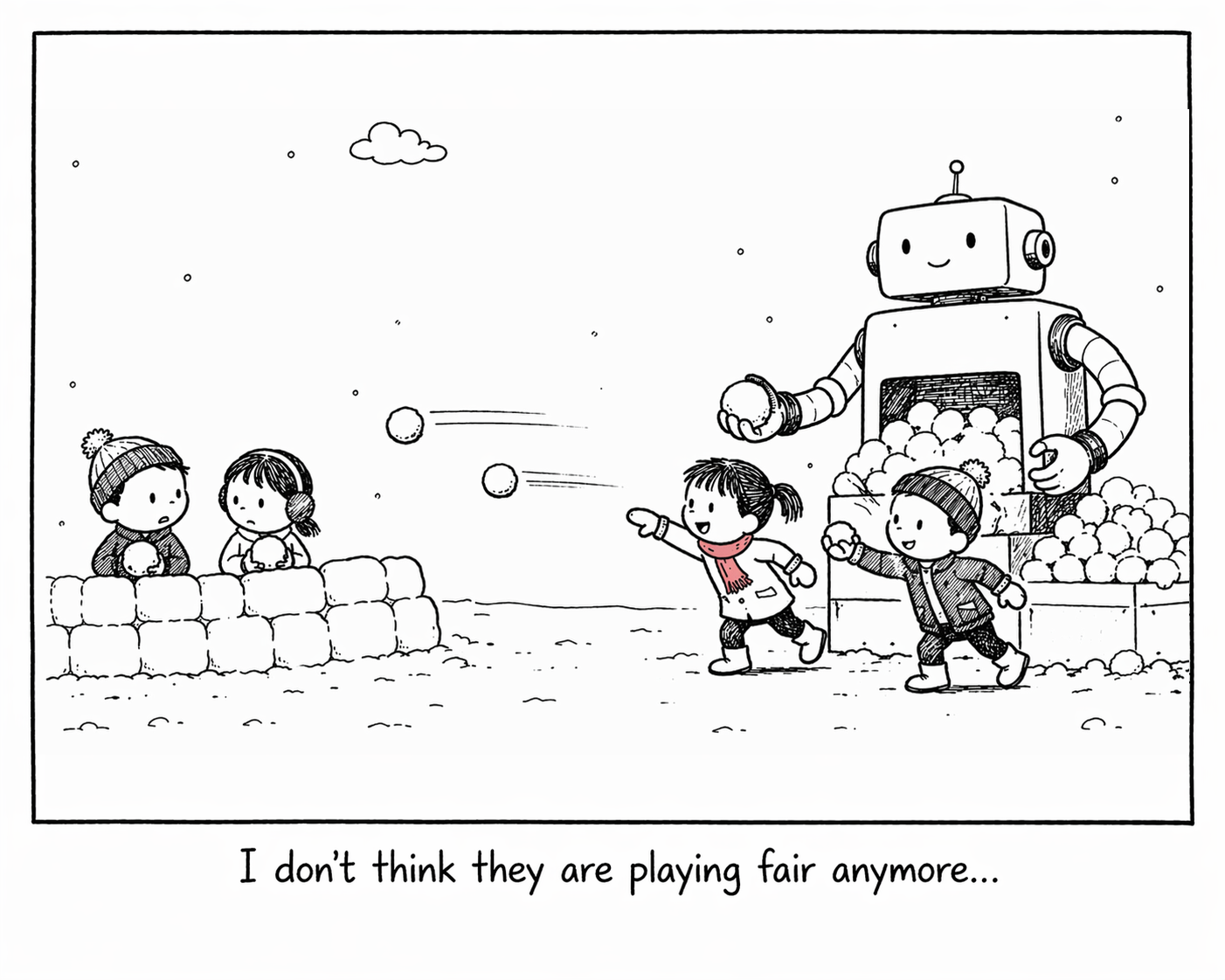
- It significantly accelerates cyber operations: tasks that once took teams weeks can now be done by a single operator in hours, raising concerns among global regulators.
- Access is tightly restricted for defensive use, but risks of misuse and proliferation remain, especially after reports of a related data breach.
- The main risk isn’t new vulnerabilities, but faster and broader exploitation, making patching delays, legacy systems, and weaker organisations more exposed, especially in sectors like finance.
- Organisations are being pushed to respond by speeding up patching, improving coordination, and adopting automation and AI-driven defences, while maintaining strong basic security practices.
In April 2026, Anthropic announced Claude Mythos, its most capable model to date. By Anthropic’s own assessment, the model is sufficiently powerful that it has not been released freely to the public. Its emergence marks a meaningful inflection point in how cyber risk needs to be understood and managed.
Mythos is not a general purpose chatbot. It is optimised for deep software reasoning and security analysis. In practical terms, it behaves less like an assistant and more like an exceptionally capable attacker, or defender, depending on how it is used.
What Makes Mythos Different
Mythos’ significance lies in the depth and autonomy of its capabilities:- Autonomous vulnerability discovery: Given access to a large codebase, it can analyse systems end to end and surface deeply buried security weaknesses.
- Chaining of weaknesses: It can combine individually low severity flaws into a coherent attack path, a capability previously associated with highly skilled nation state teams.
- Reverse engineering from the outside: Even without source code, it can infer how deployed software works and identify exploitable weaknesses.
- Independent movement post compromise: Once initial access is achieved, it can map networks and extract data with minimal human input, compressing timelines from weeks to hours.
Access to Mythos is tightly restricted. It is available only to a small group of vetted technology partners through Anthropic’s Project Glasswing, intended to support defensive use cases such as finding and fixing vulnerabilities before adversaries exploit them. Reports of unauthorised access following a separate Anthropic data breach in late April 2026 have already highlighted the inevitable concerns around proliferation.
Why This Matters Now
The risk introduced by Mythos is not that it creates new classes of vulnerabilities. The risk is that it dramatically increases speed, scale and accessibility. Work that once required specialist teams operating over weeks can, in principle, be completed by a single operator in hours.Three factors make this particularly relevant for Australian financial institutions:
- Patching backlogs are universal: Every organisation carries un-remediated vulnerabilities. Exploitation windows that were once measured in months are narrowing sharply.
- Legacy systems are no longer protected by obscurity: Systems that relied on complexity or undocumented behaviour for protection are increasingly transparent to AI assisted analysis.
- The attacker population is broadening: Capabilities once largely confined to nation states are becoming accessible to a wider range of criminal actors.
Implications for Australian Financial Institutions
Financial institutions sit squarely in the target set for sophisticated cyber adversaries. They hold sensitive personal and financial data at scale and underpin critical economic activity. Protecting that data is not only a regulatory obligation, it is central to customer trust and market stability.AI assisted tools like Mythos have several practical implications:
- The window between vulnerability discovery and exploitation will shrink materially.
- Legacy and under patched systems will become increasingly attractive targets.
- Regulatory expectations around patching discipline and cyber resilience are likely to rise as prudential regulators respond to the changing threat environment.
How Organisations Should Be Responding
Across the sector, technology and security teams should be adjusting their posture in line with guidance from the ASD and global peers. Common themes are emerging:- Accelerating vulnerability remediation: Many organisations are reprioritising patching programs, triaging backlogs based on exploitability rather than theoretical severity, and focusing on weaknesses most likely to be targeted by AI assisted tools.
- Deepening partner engagement: Managed security service providers, cloud platforms and key vendors play a critical role in detection and response. Close coordination is becoming more important as attack timelines compress.
- Tightening patching expectations: Service level expectations that were acceptable even a year ago are increasingly insufficient. Critical and high severity vulnerabilities now demand consistently shorter remediation timeframes.
Where This Is Headed
Immediate actions help address today’s most visible risks. Looking forward, organisations will need to consider more structural changes to keep pace with the threat landscape.Key areas for consideration include:
- Automated vulnerability remediation: Manual patching processes cannot match the speed of AI assisted attacks. Greater automation in identification, prioritisation and, where appropriate, deployment will be required, with human judgement retained for high risk decisions.
- AI enabled defensive capabilities: The same techniques that accelerate attacks can be used defensively. Tools that proactively scan for weaknesses, detect anomalous behaviour and accelerate incident response will be essential to closing the speed gap.
- Third party risk management: Vendors and service providers expand the attack surface and may be used as indirect entry points. Expectations around vulnerability management and assurance will need to rise, which may require difficult conversations and, in some cases, changes to supplier relationships.
Disclaimer: This article is not legal or regulatory advice. You should seek independent advice on your legal and regulatory obligations. The views and opinions expressed in this article are solely those of the author. These views and opinions do not necessarily represent those of AMP or its staff. Artificial Intelligence Technology was used to proof-read this article.