💡 The CIA Triad (explained to non-security people)
More and more organisations are coming to the realisation that information security is a key capability. They have come to understand - sometime the hard way - that not protecting their data can have disastrous consequences on their businesses.
But as organisations explore what they need to adequately protect their assets, it very often comes a time where the scope of security becomes a question. What is the objective of the information security program? Where does it begin? And end?
To try answering these questions, security specialists have come with 3 fundamental principles that define the purposes and objectives of security: Confidentiality, Integrity and Availability - together known as the CIA Triad.
Of course, security is much more than just that, but these are the 3 concepts that every organisation must understand to ensure they have a good grasp of the challenges they must address as they try to achieve a good information security maturity.
The CIA Triad
Information Security is defined through the 3 fundamental principles of Confidentiality, Integrity and Availability - The CIA Triad.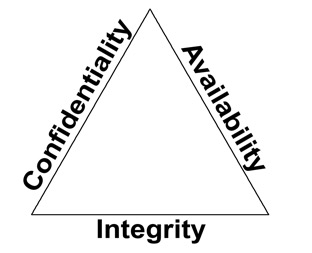
From a security perspective, the realisation of a risk is usually the result of the failure of one of these 3 tenets. For example, a data breach can be seen as a confidentiality failure, and a website being out of service can be seen as an availability issue.
Security capabilities (or “controls” ) are typically evaluated on how they address one or multiple of the three concepts. A complete security framework should adequately address each of these elements. Vulnerabilities and risks are also evaluated based on the threat they pose against one or more of these principles.
Confidentiality
Confidentiality is the prevention of the disclosure of data or information to unauthorised people or systems. Basically, making sure secrets are kept secret. This is usually done by putting in place protections such as encryption, access control, data classification etc.Integrity
Integrity is the protection of data from unauthorised modification or data corruption. Protections such as file hash, input checks and maker / checker processes typically are integrity related.Availability
Availability is the assurance that data is accessible when and where it is needed. Solutions such as system redundancy, recovery capability, backup and capacity management are typical availability protections.Priority of Confidentially, Integrity and Availability
Confidentiality, Integrity and Availability do not have the same weight and importance for each organisation. For an organisation dealing with sensitive data, confidentiality will be at the paramount of the security concerns, while a commodity company will have a strong focus on ensuring availability is maintained at all cost. Each organisation must understand these key concept and define how critical each of them is, so their security capabilities can be designed to align with the company priorities.The definition of “unauthorised”
All three aspects of the CIA Triad - Confidentiality, Integrity and Availability - try to prevent unauthorised activities in their respective domains - unauthorised access for Confidentiality, unauthorised modification for Integrity, unauthorised disruption for Availability.Non-security stakeholders have often the incorrect conception that “unauthorised” means “malicious”. They believe that information security role is to prevents attacks - from the outside or from the inside. It is only partially true. Information security role is to prevent malicious and involuntary unauthorised activities. Very often, security breaches are the result of human error, oversight, or ineptitude.
- In the case of Confidentiality, stealing passwords, capturing network traffic, extracting database content are considered as malicious attacks, while data being sent to the wrong recipient, back doors created to facilitate support, or documents left on printers are accidental events that need to be prevented too.
- Integrity would see viruses and malicious modifications to transactions as typical attacks, while incorrect inputs, incorrect code resulting in calculation errors and misconfigurations can also result in integrity incidents.
- Finally, from an Availability perspective, Denial of Services (DoS) and cryptolockers are the most common cyber-attacks faced by security professionals, but devise failure, accidental deletion and under allocation of resources are also topics that are to be adequately covered.
These misconceptions are generally reinforced by the fact that Confidentiality is very often (incorrectly) seen as the principal aspect of security.
Accidental integrity issues are often considered as operational topics, and availability issues as business continuity topics, usually managed by separate teams. There is no problem with these topics being managed by different teams, but it does change the fact that these are all security concepts, and a good security program should be able to explain how they are addressed. It is the best way for the organisation to have a complete understanding of its risks and ensure they are adequate managed.